Loki AMI User Guide

Observability shouldn’t require hours of manual setup or navigating confusing config files. At Prezelfy, we believe logging should be fast, secure, and reliable — right out of the box. That’s why we built our Loki AMI: a pre-configured, hardened Amazon Machine Image that lets you launch Loki OSS in just a few clicks.
What Do We Offer with Our Loki AMI?
Our AMI is designed to save you time, boost your security posture, and reduce the friction of standing up your own logging backend. Here’s what’s included:
- Loki OSS, pre-installed and configured
- Amazon Linux 2023, hardened using CIS Benchmarks
- Weekly rebuilt AMIs to ensure up-to-date security patches
- Preconfigured Loki config for saving logs on host machine and running on
localhost:3100 - Loki runs as a managed systemd service
- Port 3100 pre-opened in the firewall for Loki access
- SSH access locked down and only enabled if launched with your own key pair
- System directories and permissions configured for secure operation
In short: launch and log — without the operational overhead.
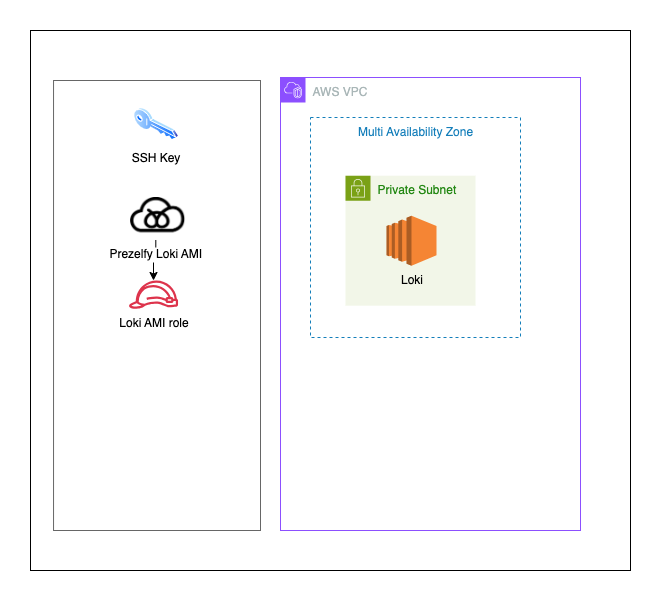
Architectural Design
The Prezelfy Loki AMI is designed around three key principles: security, simplicity, and scalability. It works just as well on a t3.medium for testing as it does as part of a larger observability platform — without the need for manual patching or complex configuration.
Whether you’re collecting logs from EC2, containers, or your own apps, the architecture ensures that Loki is lightweight, isolated, and ready to integrate with your AWS infrastructure and applications.
Key design highlights:
- Stateless Setup: Loki stores logs locally on host but does not persist configuration from external sources. The default
loki.ymlis editable via SSH. - Security First: SSH is disabled or restricted by keypair. Only port 3100 is open by default.
- Systemd-Based: Loki runs as a service, ensuring automatic startup and restart on failure.
- Firewall-Managed Access:
firewalldis enabled and pre-configured, with strict control over exposed ports. - Up-to-Date: Each week, we publish a fresh AMI with all system and Loki updates included. No patching needed on your end.
Whether you're collecting logs from a single EC2 instance or integrating with Grafana, this AMI gives you a lightweight, reliable foundation to build on.
If you’re visual — here’s how it all fits together:
Installation Guide: How to Launch
You don’t need to install anything or resolve dependencies — just launch and collect logs.
Steps:
- Generate a Key Pair
Follow the AWS EC2 docs to create a key pair and securely store the private key. - Launch the AMI
- Subscribe to the AMI on AWS Marketplace
- Create a new EC2 instance using the AMI
- Attach your SSH key pair (optional, for admin access)
- Choose a security group that allows access to port 3100 only from trusted sources, such as:
- Your office IP (e.g.,
203.0.113.5/32) - Your VPN network (e.g.,
198.51.100.0/24) - A private CIDR inside your VPC (e.g.,
10.0.0.0/16)
- Your office IP (e.g.,
- Avoid exposing port 3100 to
0.0.0.0/0unless you secure it with a reverse proxy
- Access Loki via HTTP
http://<your-ec2-instance-public-ip>:3100/ready - Optional SSH Access
ssh -i your-key.pem ec2-user@<your-ec2-instance-public-ip>
How to Use Loki?
Once you're connected, Loki works just like any other OSS deployment. You can:
- Push logs to Loki instance
- Connect Loki to Grafana for UI access. You can launch Grafana in only few steps
- View Loki health under `/ready
- Manually edit
/etc/loki/loki.ymlto add or change storage (like S3 and DynamoDB) - Restart the service with
sudo systemctl restart loki - Integrate with Grafana
- Configure Loki in Grafana
Your data stays in your environment — our AMI just gives you the platform to collect and act on it.
Troubleshooting: Loki Not Working?
Can’t reach the Loki?
- Make sure port 3100 is open in your EC2 security group for your current IP address or network
- Use an SSH tunnel if you want to keep port 3100 entirely private
Loki service isn’t running?
- SSH into the instance and run:
sudo systemctl status loki
Need to update your targets?
- SSH into the instance
- Edit
/etc/loki/loki.yml - Restart the service:
sudo systemctl restart loki
Still stuck?
Reach out to support@prezelfy.com — we’re happy to help.
Ready to Launch?
You can get started on AWS Marketplace today. The Prezelfy Loki AMI is built for speed, security, and simplicity — so you can stop worrying about setup and start focusing on what your logs are telling you.